Articles
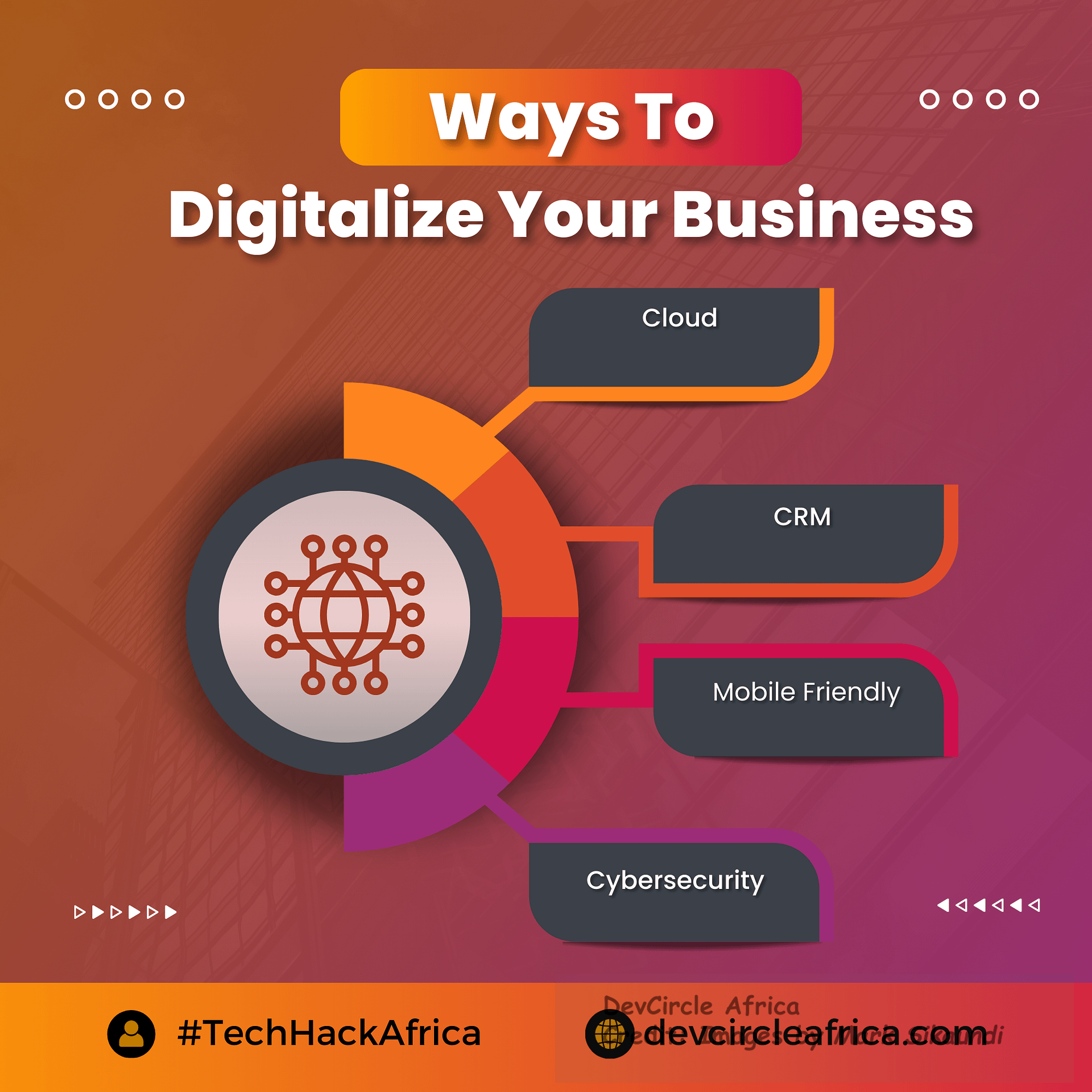
The Power of Cloud CRM: 4 Mobile-Friendly Solutions for Airtight Cybersecurity
Articles
Free WordPress Themes

Top 10 Free WordPress Themes for Beginners
Are you just starting out with WordPress and looking for a free theme to get your website up and running? Look no further! In this post, we have compiled a list of the top 10 free WordPress themes that are perfect for beginners.
Table of Contents
1. Astra – Astra is a lightweight and customizable theme that offers plenty of options for customization. It is perfect for users who want to create a professional-looking website without having to spend a lot of time on design.
2. OceanWP – OceanWP is a highly versatile theme that can be used for a wide range of websites. It comes with a variety of pre-designed templates and customization options, making it easy to create a unique and professional-looking website.
3. Neve – Neve is a clean and minimalistic theme that is perfect for users who want a simple and elegant design. It offers a range of customization options, making it easy to create a website that reflects your personal style.
4. Zerif Lite – Zerif Lite is a one-page theme that is perfect for users who want to create a sleek and modern website. It offers a range of customization options, making it easy to create a website that stands out from the crowd.
5. Hestia – Hestia is a multipurpose theme that is perfect for users who want to create a professional-looking website for their business. It offers a range of customization options, making it easy to create a website that meets your specific needs.
6. Sydney – Sydney is a powerful business theme that is perfect for users who want to create a professional-looking website. It offers a range of customization options, making it easy to create a website that stands out from the competition.
7. ColorMag – ColorMag is a magazine-style theme that is perfect for users who want to create a content-rich website. It offers a range of customization options, making it easy to create a website that is both visually appealing and easy to navigate.
8. Ashe – Ashe is a clean and minimalistic theme that is perfect for users who want to create a simple and elegant website. It offers a range of customization options, making it easy to create a website that reflects your personal style.
9. Zillah – Zillah is a modern and stylish theme that is perfect for users who want to create a visually appealing website. It offers a range of customization options, making it easy to create a website that stands out from the crowd.
10. Shapely – Shapely is a one-page theme that is perfect for users who want to create a sleek and modern website. It offers a range of customization options, making it easy to create a website that is both visually appealing and easy to navigate.
These are just a few of the top free WordPress themes that are perfect for beginners. With so many options to choose from, you are sure to find a theme that suits your personal style and website needs.
How to Choose the Right Free WordPress Themes for Your Website
Choosing the right free WordPress theme for your website can be a daunting task, especially with so many options to choose from. In this post, we will discuss some key factors to consider when selecting a theme that best suits your needs.
1. Design and Layout – The design and layout of a theme play a crucial role in the overall look and feel of your website. Consider the aesthetic appeal of the theme and how it aligns with your brand and target audience. Look for a theme that offers a clean and modern design with a layout that is easy to navigate.
2. Customization Options – Customization options are essential for creating a unique and personalized website. Look for themes that offer a range of customization options, such as customizable headers, colors, fonts, and layouts. This will allow you to tailor the theme to your specific needs and preferences.
3. Responsive Design – With more and more users accessing websites on mobile devices, it is essential to choose a theme that offers a responsive design. A responsive theme will adapt to different screen sizes, ensuring that your website looks great on all devices.
4. SEO-Friendly – Search engine optimization (SEO) is crucial for improving your website’s visibility in search engine results. Look for themes that are SEO-friendly and optimized for search engines. This will help increase your website’s rankings and drive more traffic to your site.
5. Support and Updates – Choose a theme that offers reliable support and regular updates. This will ensure that your theme remains secure, compatible with the latest WordPress updates, and free of bugs or issues. Check for theme documentation, forums, and support channels to ensure that you can easily get help when needed.
6. Plugins Compatibility – Consider the compatibility of the theme with popular WordPress plugins. Many themes offer built-in support for popular plugins such as WooCommerce, Yoast SEO, or Contact Form 7. This will allow you to extend the functionality of your website and add important features without any compatibility issues.
By considering these key factors, you can choose the right free WordPress theme that best suits your website needs and helps you create a professional and visually appealing website.
The Benefits of Using Free WordPress Themes
Free WordPress themes offer numerous benefits to users looking to create a website without breaking the bank. In this post, we will discuss some of the key advantages of using free themes for your WordPress website.
1. Cost-Effective – One of the most significant advantages of using free WordPress themes is that they are cost-effective. With free themes, you can create a professional-looking website without having to spend a dime on design or development. This is particularly beneficial for small businesses, startups, or individuals on a tight budget.
2. Easy to Customize – Free WordPress themes often come with a range of customization options that allow you to tailor the theme to your specific needs and preferences. With simple customization tools, you can easily change colors, fonts, layouts, and more to create a unique and personalized website that reflects your brand identity.
3. Wide Variety of Options – There are thousands of free WordPress themes available, offering a wide variety of designs, layouts, and features to choose from. Whether you are looking for a simple and minimalistic theme or a feature-rich business theme, you are sure to find a free theme that suits your website needs.
4. Community Support – Many free WordPress themes come with built-in support forums, documentation, and tutorials that can help you get started and troubleshoot any issues you may encounter. The WordPress community is also a valuable resource for finding tips, advice, and solutions to common problems.
5. Regular Updates – Free themes are often updated regularly to ensure compatibility with the latest WordPress versions and plugins. By using a free theme, you can rest assured that your website will remain secure, up-to-date, and free of bugs or issues.
6. Beginner-Friendly – Free WordPress themes are perfect for beginners who are just starting with WordPress and may not have experience with web design or development. With user-friendly customization options, pre-designed templates, and easy-to-use tools, you can create a professional-looking website in no time.
Overall, free WordPress themes offer a cost-effective, customizable, and beginner-friendly solution for creating a website that meets your specific needs and budget. With so many benefits to using free themes, you can create a stunning website that showcases your brand identity and attracts visitors to your site.
Articles
The Importance of SEO Optimization for Personal Trainers
SEO, or search engine optimization, plays a crucial role in today’s digital age, especially for personal trainers looking to grow their online presence. By optimizing your website and content for search engines, you can increase your visibility and reach a broader audience of potential clients. Here are a few reasons why SEO optimization is essential for personal trainers:
1. Increased visibility: By implementing SEO best practices on your website, you can improve your search engine rankings and make it easier for potential clients to find you online. This increased visibility can help drive more traffic to your website and ultimately generate more leads for your business.
2. Targeted traffic: SEO allows you to target specific keywords and phrases that are relevant to your services as a personal trainer. By optimizing your content for these keywords, you can attract highly targeted traffic that is more likely to convert into paying clients.
3. Competitive advantage: In a crowded market of personal trainers, SEO optimization can give you a competitive edge by helping you stand out from the competition. By ranking higher in search engine results, you can establish yourself as a trusted authority in your field and attract more clients to your business.
Overall, SEO optimization is crucial for personal trainers who want to grow their online presence and attract more clients. By implementing best practices and staying up to date with the latest trends in SEO, you can position yourself for success in the digital age.
In today’s digital world, having a strong online presence is essential for personal trainers looking to grow their business. One of the most effective ways to improve your online visibility is through SEO optimization. Here are a few key reasons why SEO is important for personal trainers:
1. Increase brand awareness: SEO optimization can help boost your brand visibility online, making it easier for potential clients to find you when searching for personal training services. By ranking higher in search engine results, you can increase awareness of your brand and attract more clients to your business.
2. Build credibility and trust: When your website ranks high in search engine results, it signals to potential clients that you are a credible and trustworthy source of information. This can help build trust with potential clients and increase the likelihood that they will choose you as their personal trainer.
3. Drive more traffic to your website: SEO optimization can help drive more organic traffic to your website, increasing the chances of converting visitors into paying clients. By optimizing your content for relevant keywords and phrases, you can attract more qualified leads to your business and ultimately grow your client base.
Overall, SEO optimization is a valuable tool for personal trainers looking to expand their online presence and attract more clients. By implementing SEO best practices and staying current with the latest trends, you can position yourself for success in the competitive world of online personal training.
Articles
The Importance of Continuous SEO Training in Zambia
In today’s digital age, having a strong online presence is crucial for the success of any business. Search Engine Optimization (SEO) plays a key role in helping businesses improve their visibility on search engine results pages, driving more traffic to their websites and ultimately increasing their revenue. As the digital landscape continues to evolve, it is important for businesses in Zambia to invest in continuous SEO training to stay ahead of the competition.
SEO algorithms are constantly changing, and what may have worked well in the past may no longer be effective. By investing in continuous SEO training, businesses in Zambia can stay up-to-date on the latest trends and best practices in the industry. This allows them to make informed decisions and make necessary adjustments to their SEO strategies to ensure they are maximizing their online visibility.
Continuous SEO training also allows businesses to develop a deeper understanding of how search engines work and how customers search for products and services online. This insight can help businesses tailor their SEO strategies to better meet the needs and preferences of their target audience, ultimately driving more qualified traffic to their websites.
In addition, continuous SEO training can help businesses in Zambia avoid costly mistakes that can negatively impact their search engine rankings. By learning the latest techniques and strategies for improving SEO, businesses can ensure they are following best practices and making the most of their online presence.
Overall, investing in continuous SEO training is essential for businesses in Zambia to stay competitive in the digital marketplace. By staying informed on the latest SEO trends and best practices, businesses can improve their online visibility, drive more traffic to their websites, and ultimately increase their revenue. So, if you’re running a business in Zambia, make sure to prioritize continuous SEO training to stay ahead of the curve and achieve success in the digital world.
-
SEO2 months ago
How to Increase Conversion Rate in 2024: 15 Effective Strategies
-
SEO2 months ago
What is SEO and how it works
-
SEO2 months ago
Is Google Keyword Planner worth it?
-
GamersX2 months ago
Call of Duty: Black Ops 6 Officially Announced, Full Reveal on June 9
-
SEO2 months ago
Tips for Successful SEO Optimization for Personal Trainers
-
Artificial Intelligence2 months ago
Musk lumps OpenAI and Apple together
-
SEO2 months ago
Which is better, Google Keyword Planner or SEMrush?
-
Technical Writing2 months ago
Why You Should Invest in SEO Training in Zambia











